The ultimate guide to penetration testing
Last updated 25 May 2026
Could your business survive a targeted cyber attack? With cybercriminals becoming more sophisticated and attacks growing more devastating, no organisation is immune.
Global cybercrime is now estimated to cost around $10.5 trillion, making it one of the largest economic threats worldwide. The cost of a single data breach also remains significant, with an average loss of $4.45 million globally, not to mention the damage to customer trust and the operational disruption that follows.
Penetration testing, also known as ethical hacking, is one of the most effective ways to identify vulnerabilities before attackers exploit them.
In this environment, traditional security measures are no longer enough on their own. Penetration testing goes beyond passive defences by uncovering hidden weaknesses and showing how attackers could gain access to your systems.
In this guide, we’ll cover:
With over 28 years of experience in cyber security, The Missing Link has helped organisations across Australia uncover weaknesses, strengthen defences, and build long-term resilience.
Is your business ready?

What is penetration testing?
The evolving cyber threat landscape
The rise of digital transformation has brought unprecedented efficiency to businesses, but it has also increased their exposure to cyber threats. As organisations adopt cloud platforms, enable remote work, and connect more systems, the number of potential entry points for attackers continues to grow.
According to Verizon’s Data Breach Investigations Report, 74% of breaches involve the human element, including phishing, stolen credentials, and user error. This highlights how attackers are not just targeting systems, but the people and processes around them.
At the same time, the financial impact of these attacks remains high, reinforcing the need for stronger, more proactive security measures.
What exactly is penetration testing?
Penetration testing is a controlled cyber security assessment that simulates real-world attacks to identify and exploit vulnerabilities before attackers can.
Unlike automated vulnerability scanning, which identifies potential risks, penetration testing takes this a step further by attempting to exploit those weaknesses. This provides a more realistic view of how vulnerabilities could be used to gain unauthorised access to sensitive data or critical systems.
This hands-on approach helps organisations:
-
-
Identify weak points across their environment
-
Understand how vulnerabilities could be exploited in practice
-
Prioritise remediation based on real risk
-
Strengthen defences against real-world attack scenarios
-
Penetration testing can be conducted across a range of environments, including networks, web applications, cloud platforms, and end-user systems, giving organisations a comprehensive view of their security posture.
Why penetration testing matters
Penetration testing has become a key component of modern cyber security strategies because it reflects how attackers actually operate.
Rather than relying solely on preventative controls, organisations can test their defences under realistic conditions, uncover hidden vulnerabilities, and address them before they are exploited.
At The Missing Link, our approach is grounded in real-world expertise. As one of Australia’s only CVE Numbering Authorities, we contribute to the identification and disclosure of new vulnerabilities, giving us a deep understanding of emerging threats and how they can impact your business.
In short, penetration testing identifies how attackers could access your systems and what they could achieve once inside.
Case study
How Kennards Hire strengthened their cyber security
With the shift to remote operations and an increasingly complex threat landscape, Kennards recognised the need for more proactive security measures. Through comprehensive penetration testing and a detailed security review, The Missing Link identified vulnerabilities that could have impacted critical systems and day-to-day operations.
These insights informed a more robust security strategy, helping to reduce the risk of data breaches and operational disruption. As a result, Kennards Hire has been able to maintain business continuity while protecting both customer and operational data.
This transformation highlights how proactive penetration testing can reduce risk and improve resilience in complex environments.
Penetration testing vs vulnerability assessments
While both vulnerability assessments and penetration testing are essential, they serve different purposes.
Vulnerability assessments use automated tools to identify known weaknesses across systems and applications. They provide a broad, surface-level view of potential risks and are useful for ongoing monitoring.
Penetration testing builds on this by going deeper. It involves actively attempting to exploit identified vulnerabilities to understand their real-world impact and how an attacker could move through an environment.
In simple terms:
-
-
Vulnerability assessments identify potential weaknesses
-
Penetration testing tests how those weaknesses could be exploited
-
The difference between the two approaches is simple, but important:
-png.png?width=571&height=342&name=Vulnerability%20assessment%20vs%20penetration%20testing%20(1)-png.png)
Figure: Vulnerability assessments identify potential risks, while penetration testing validates how those risks can be exploited in real-world scenarios.
Used together, they provide a more complete view of your security posture.
At The Missing Link, we integrate both approaches into our cyber security strategies, giving you visibility across both immediate risks and deeper, more complex attack paths. This allows you to prioritise remediation and make more informed decisions about how to strengthen your defences.
Why is penetration testing important for businesses?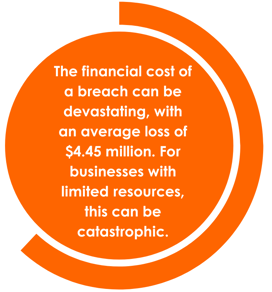
Cyber threats continue to impact organisations of all sizes. According to the Australian Cyber Security Centre (ACSC), cybercrime reports increased by 23% in the last financial year, highlighting the growing volume of attacks targeting Australian businesses
Small businesses are often seen as easier targets due to limited internal resources, while larger organisations face increased exposure because of their complex systems and extensive digital assets. In both cases, the risk is not just the attack itself, but the potential financial, operational, and reputational impact that follows.
Penetration testing plays an essential role in helping businesses stay ahead of these risks. By simulating real-world attack scenarios, organisations can expose security gaps early and take action before they are exploited.
Regardless of size, regular penetration testing and vulnerability scanning can significantly reduce the likelihood and impact of a breach. Rather than reacting to incidents after they occur, businesses can take a more proactive approach to strengthening their security posture.
Different types of businesses face unique challenges when it comes to cyber security:
-
Small businesses: With limited resources, they are attractive targets for attackers. Penetration testing helps uncover vulnerabilities early, reducing the risk of financial damage and operational disruption.
-
Medium-sized businesses: As organisations grow, so does the complexity of their IT environments. Regular testing ensures security controls keep pace with expansion and evolving threats.
-
Large enterprises: Regular testing is often required for regulatory compliance, particularly in industries such as finance and healthcare. It also helps secure large, distributed networks and maintain customer trust.
In short, penetration testing enables businesses to proactively identify and address risks before they become real incidents.
What are the different types of penetration testing?
Penetration testing is not a one-size-fits-all solution. Each test is designed to identify specific vulnerabilities across systems, networks, and even the physical infrastructure of an organisation.
By replicating how attackers operate, penetration testing provides valuable insight into how well a business can defend itself. Given the complexity of today’s threat landscape, organisations need a tailored approach that reflects their unique environment, risk profile, and operational priorities.
By focusing on different areas such as networks, applications, wireless systems, and even human behaviour, businesses can ensure their entire security posture is properly assessed.
Network penetration testing
Network penetration testing assesses the security of both internal and external network environments. Attackers often target network vulnerabilities to gain unauthorised access, disrupt services, or move laterally across systems.

- External network testing focuses on public-facing systems such as firewalls, servers, and routers. These are common entry points for attackers attempting to exploit misconfigurations, weak credentials, or unpatched software.
- Internal network testing evaluates what could happen if an attacker gained access to the network. This includes testing for weak segmentation, excessive privileges, and the ability to move between systems.
This type of testing helps uncover weaknesses in network design and configuration, providing clear recommendations to strengthen overall security.
At The Missing Link, our penetration testing engineers specialise in identifying vulnerabilities across both external and internal network environments, helping you secure critical assets before they can be exploited.
Web application penetration testing
Web applications are a common target for attackers because they often process sensitive data such as customer information and payment details.
Web application penetration testing focuses on identifying vulnerabilities within web-based systems, including:
-
SQL Injection: Allows attackers to manipulate backend databases, potentially leading to data theft or system compromise.
-
Cross-Site Scripting (XSS): Enables attackers to inject malicious scripts into web pages, potentially leading to session hijacking or data exposure.
-
Authentication and access control weaknesses: Poorly implemented login and session controls can allow unauthorised access to user accounts or administrative functions.
A thorough web application penetration test simulates these attack methods to assess how well the application can withstand real-world threats.
The Missing Link uses advanced tools and real-world testing techniques to identify and remediate vulnerabilities before they result in costly breaches.
Wireless penetration testing
As organisations increasingly rely on wireless networks, they also introduce additional security risks.
Wireless penetration testing examines Wi-Fi networks to identify weaknesses in encryption, access controls, and network configuration.
Common risks include:
-
-
Weak or outdated encryption protocols
-
Poor network segmentation
-
Misconfigured access points
-
If exploited, these vulnerabilities can allow attackers to intercept communications, access internal systems, or launch further attacks.
The Missing Link conducts wireless assessments and site surveys to ensure your network is configured securely and aligned with best practices.
Social engineering and human vulnerabilities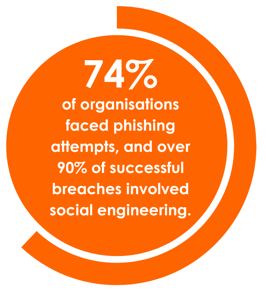
While technical controls are critical, the human element remains one of the most common entry points for attackers.
Social engineering testing simulates real-world tactics such as phishing, impersonation, and phone-based attacks to assess how employees respond.
According to IBM, it takes an average of 277 days to identify and contain a data breach. This extended window gives attackers time to move through systems, escalate access, and cause significant damage before being detected.
By testing how users and systems respond to these types of attacks, organisations can identify gaps in both awareness and detection capabilities.
The Missing Link incorporates phishing simulations and social engineering techniques into its penetration testing services, helping you strengthen your human firewall and build a more security-aware culture.
Physical penetration testing
Cyber security extends beyond digital systems. Physical penetration testing evaluates how well your organisation’s physical security controls can prevent unauthorised access.
This includes testing scenarios such as:
-
-
Attempting to access restricted areas
-
Bypassing access controls
-
Exploiting weaknesses in surveillance or building security
-
This type of testing is particularly important for organisations handling sensitive data or operating in regulated industries.
By identifying gaps in physical security, businesses can ensure their environments are protected from both digital and real-world threats.
Cloud native security and penetration testing
Cloud environments now play a central role in how businesses operate. As organisations migrate systems, applications, and data to the cloud, ensuring these environments are secure becomes essential.
Penetration testing plays an important role in this process by helping organisations identify and address vulnerabilities within cloud environments before they can be exploited.
Cloud penetration testing assesses how vulnerabilities in cloud environments could be exploited across infrastructure, applications, and configurations. This provides a clearer understanding of how an attacker could gain access to sensitive data or disrupt services.
Penetration testing in cloud environments can be applied across several key areas:
-
-
Cloud-based applications: Ensuring applications hosted in the cloud are protected against common vulnerabilities such as injection attacks and authentication weaknesses.
-
Cloud-based infrastructure: Assessing the security of virtual machines, containers, and supporting services to identify misconfigurations or excessive permissions.
-
Cloud-based data storage: Evaluating how data is stored, accessed, and protected to reduce the risk of unauthorised access or exposure.
-
Cloud-based networks: Reviewing network configurations, access controls, and communication pathways within the cloud environment.
-
This approach provides several important benefits:
-
-
Identification of vulnerabilities: Uncovering weaknesses across cloud systems before they are exploited.
-
Remediation of security risks: Providing clear, actionable recommendations to address identified issues.
-
Ensuring data security: Helping safeguard sensitive information from breaches or unauthorised access.
-
Compliance: Assisting organisations in meeting industry and regulatory standards for cloud security.
-
By integrating cloud penetration testing into their broader cyber security strategy, businesses can strengthen the resilience of their cloud environments and better protect against evolving threats.
How does penetration testing work?
The penetration testing process explained
Penetration testing is not a one-size-fits-all solution. Different tests are designed to target specific vulnerabilities across systems, networks, and infrastructure. By testing how an attacker could gain access and move through systems, penetration testing provides valuable insight into how well a business can defend itself.
Most penetration tests follow a structured process, designed to reflect how attackers operate in real-world scenarios.
Penetration testing involves several key phases:

Figure: The key phases of a penetration test, from initial reconnaissance through to reporting.
-
-
Reconnaissance: Gathering information to identify potential weak points, such as open ports or exposed services.
-
Scanning: Mapping systems and identifying vulnerabilities that could act as entry points.
-
-
-
-
Exploitation: Attempting to exploit identified vulnerabilities using real-world attack techniques.
-
Post-Exploitation: Simulating how an attacker would move within the environment after gaining access.
-
-
-
-
-
Reporting: Documenting findings, impacts, and recommended remediation actions.
-
-
Each phase builds on the previous one, providing a realistic view of how an attack could unfold and where defences may fail.
1. Planning and reconnaissance
This foundational phase sets the direction for the entire test. The penetration testing team works with your organisation to define scope, objectives, and areas of focus.
Reconnaissance involves both passive and active information gathering:
-
-
Passive reconnaissance: Collecting publicly available information such as domain records, employee data, or exposed services.
-
Active reconnaissance: Interacting directly with systems to identify open ports, services, and potential vulnerabilities.
-
The goal is to uncover as many potential entry points as possible before testing begins.
2. Scanning and identifying entry points
Once initial information is gathered, testers begin scanning the environment to reveal potential attack paths and map the network.
Common tools used in this phase include:
-
-
Nmap for network discovery and port scanning
-
Nessus for identifying known vulnerabilities
-
OpenVAS for detecting misconfigurations and weaknesses
-
This phase provides a detailed picture of the environment and highlights the most likely paths an attacker could take.
At The Missing Link, we combine automated tools with manual validation to ensure results are accurate and relevant.
3. Exploitation: Simulating real-world attacks
With vulnerabilities identified, testers attempt to exploit them to demonstrate what an attacker could achieve.
This is where the real risk becomes clear. Testers simulate techniques such as:
-
-
SQL injection to access backend databases
-
Cross-site scripting (XSS) to compromise user sessions
-
Authentication bypass to gain unauthorised access
-
Exploitation path: How attackers move through systems
.png?width=687&height=643&name=Exploit%20path%20(1).png)
Figure: Example attacker pathway, from initial breach through to data access
As shown above, attackers typically move through stages such as:
-
-
Initial breach
-
Lateral movement
-
Privilege escalation
-
Data access or system control
-
This phase demonstrates not just where vulnerabilities exist, but how they can be chained together to create a full attack path.
4. Post-Exploitation: Understanding the impact
Once access is gained, testers simulate how far an attacker could move within the environment.
This includes testing:
-
-
Persistence: Maintaining access through backdoors or newly created accounts
-
Lateral movement: Navigating between systems to expand access
-
Privilege escalation: Gaining higher-level permissions to access sensitive data
-
At The Missing Link, this phase is where we focus on helping you understand the true impact of a potential breach. Rather than stopping at initial access, our testers simulate how an attacker would progress through your environment, identifying how vulnerabilities can be chained together to reach critical systems and data.
This approach gives you a clearer picture of not just how an attack could happen, but what an attacker could achieve once inside your environment.
5. Reporting: Turning findings into action
The final phase is reporting, where all findings are documented and prioritised.
A penetration testing report typically includes:
-
-
A detailed explanation of each vulnerability
-
The potential business impact
-
Severity ratings to guide prioritisation
-
Clear, actionable remediation steps such as patching, reconfiguration, or implementing new security controls.
-
At The Missing Link, we go beyond identifying vulnerabilities. We work closely with you to translate findings into a practical action plan that strengthens your overall security posture.
In short, penetration testing helps you find and fix vulnerabilities before they become real incidents.

The importance of regular penetration testing
Why regular testing is essential
Cyber threats are constantly evolving, making one-time security checks inadequate. Regular penetration testing, combined with vulnerability scanning, helps businesses stay ahead of attackers by continuously identifying new vulnerabilities as they emerge.
By simulating real-world attack scenarios, organisations can refine their security posture over time, rather than relying on outdated assumptions about their environment.
The risks of one-time testing
A single penetration test provides only a snapshot of a business’s security at a specific point in time. As systems change, new technologies are introduced, and threats evolve, new vulnerabilities can emerge that were not present during the initial test.
According to Verizon’s Data Breach Investigations Report, exploitation of vulnerabilities remains one of the leading methods attackers use to gain initial access. This reinforces the need to continuously identify and address weaknesses before they can be exploited.
Relying on outdated results can leave businesses blind to current risks and increasingly vulnerable to attack.
At The Missing Link, our penetration testing services are designed to evolve alongside your environment. By offering ongoing testing schedules tailored to your organisation, we help ensure your security controls remain effective against emerging threats.
How often should you test?
The frequency of penetration testing depends on several factors, including business size, industry requirements, and how often systems are updated.
-png.png?width=499&height=293&name=Penetration%20testing%20frequency%20(1)-png.png)
Figure: Recommended penetration testing frequency based on business size and complexity.
General guidelines include:
-
Small businesses: Annual testing is typically sufficient, unless significant infrastructure changes occur.
-
Medium-sized businesses: As environments grow in complexity, bi-annual or quarterly testing helps ensure new systems and applications remain secure.
-
Large enterprises: Organisations operating in sectors such as finance, healthcare, or retail often require quarterly or even monthly testing to meet compliance and security requirements.
-
Post-major updates: Any significant update, such as cloud migration, new system deployment, or infrastructure changes, should be followed by penetration testing to identify newly introduced risks.
The Missing Link offers flexible testing schedules tailored to your business, ensuring your security remains aligned with both operational changes and the evolving threat landscape.
Case study
How MedHealth enhanced cyber security with penetration testing
Challenge: Increased security complexity following rapid growth through acquisitions.
Result: Strengthened security posture, improved compliance, and achieved ISO27001 certification.
MedHealth, a healthcare provider with over 2,000 employees, partnered with The Missing Link after rapid growth through acquisitions, which introduced increased security complexity across their environment.
To address this, The Missing Link conducted a comprehensive security review and developed a two-year roadmap, including regular penetration testing, firewall upgrades, and improved endpoint compliance.
These initiatives strengthened MedHealth’s security posture, safeguarded sensitive healthcare data, and supported the organisation in achieving ISO27001 certification.
Ongoing testing and continuous improvement now ensure MedHealth remains resilient and compliant as its environment evolves.
This transformation highlights how a structured, long-term approach to penetration testing can improve security and support compliance in complex environments.
Aligning Penetration Testing with security frameworks
In Australia, businesses must comply with a range of security frameworks and standards. Regular penetration testing plays an important role in assessing whether security controls are effective and aligned with these requirements.
Key frameworks include:
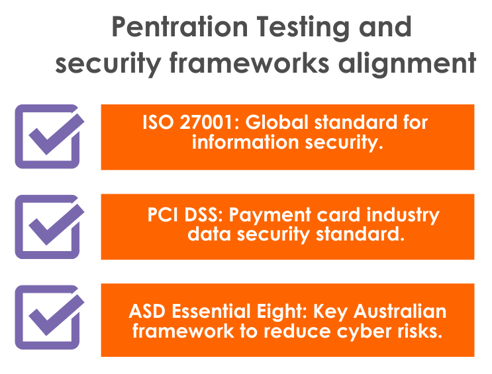 Figure: Common security frameworks supported by penetration testing, including ISO 27001, PCI DSS, and the ASD Essential Eight.
Figure: Common security frameworks supported by penetration testing, including ISO 27001, PCI DSS, and the ASD Essential Eight.
-
-
ISO 27001: A global standard for information security management. Penetration testing supports its continuous improvement approach by validating that security controls remain effective over time.
-
-
-
PCI DSS: The Payment Card Industry Data Security Standard applies to organisations handling cardholder data. Regular penetration testing is required to help secure payment systems and protect sensitive financial information.
-
-
-
ASD Essential Eight: The Australian Signals Directorate’s Essential Eight outlines key strategies to reduce cyber risk. Penetration testing helps organisations assess their maturity and strengthen defences against threats such as ransomware.
-
The Missing Link’s penetration testing services help businesses align with these frameworks, improving security while supporting compliance with Australian standards.
Penetration testing as a compliance requirement
Penetration testing is not just a best practice. For many organisations, it is also a regulatory expectation.
For example, financial services providers must comply with regulations such as APRA CPS 234, which requires organisations to maintain strong information security controls and regularly test their effectiveness.
Healthcare providers must also meet obligations under the Australian Privacy Principles (APP), ensuring sensitive patient information is properly protected.
At The Missing Link, we deliver penetration testing services that help organisations meet these requirements while strengthening their overall security posture.
Key benefits of penetration testing
How penetration testing strengthens your cyber defences
Penetration testing is a proactive method for uncovering vulnerabilities in your IT systems before attackers can exploit them. By replicating attacker behaviour, it goes beyond traditional security measures, identifying gaps in detection, response, and compliance to strengthen your overall security posture.
 Figure: Key benefits of penetration testing, from identifying vulnerabilities to improving security maturity.
Figure: Key benefits of penetration testing, from identifying vulnerabilities to improving security maturity.
1. Identifying unknown vulnerabilities
Even well-protected systems can contain hidden weaknesses. Regular penetration testing helps uncover these vulnerabilities before they are exploited, allowing you to address them early.
2. Preventing costly breaches and downtime
Cyber incidents can result in significant financial loss and operational disruption. By identifying vulnerabilities early, penetration testing helps reduce the likelihood of successful attacks and minimises downtime.
Rather than reacting to incidents after they occur, businesses can take a proactive approach to protecting critical systems and maintaining continuity.
3. Improving incident response
Penetration testing helps organisations evaluate how effectively they detect and respond to threats.
By identifying gaps in monitoring, alerting, and response processes, businesses can strengthen their incident response plans and ensure teams are better prepared to act during a real-world attack.
At The Missing Link, we incorporate post-test insights to help refine response strategies and improve overall readiness.
4. Enhancing security maturity
Security is not static. As threats evolve, so must your defences.
Regular penetration testing supports ongoing improvement by validating the effectiveness of existing controls and identifying areas for enhancement. Frameworks such as the ASD Essential Eight reinforce the importance of continuous testing as part of building a mature and resilient security posture.
ROI of penetration testing
Investing in penetration testing delivers measurable value by reducing risk and helping organisations avoid the costs associated with cyber incidents.
Key areas of return include:
-
-
Cost avoidance: Identifying vulnerabilities early helps prevent breaches, reducing the financial impact of incidents and downtime.
-
Regulatory compliance: Regular testing supports compliance with standards such as ISO 27001, PCI DSS, and industry-specific requirements.
-
Risk reduction: By proactively addressing vulnerabilities, organisations reduce their overall attack surface and exposure.
-
Stronger security posture: Continuous testing ensures security controls remain effective as systems and threats evolve.
-
Rather than viewing penetration testing as a one-off cost, it should be considered an ongoing investment in protecting your systems, data, and reputation.
The Missing Link's unique approach to penetration testing
Why choose The Missing Link
The Missing Link delivers tailored penetration testing solutions designed to identify and address vulnerabilities before they can be exploited.
As one of the few Australian organisations with CVE Numbering Authority (CNA) status, and the only dedicated penetration testing firm among them, we bring a unique level of expertise to every engagement. Our team holds industry-recognised certifications, including OSCP, OSWE, and CISSP, ensuring your testing is conducted to the highest technical standard.
This allows us to identify vulnerabilities that are often missed by standard testing approaches.
Certified expertise and industry leadership
Our penetration testing is delivered by CREST-approved teams, following globally recognised ethical and technical standards.
We combine manual testing with advanced tooling to simulate real-world attack scenarios, uncovering vulnerabilities that automated scans alone may miss. Our involvement in identifying and disclosing zero-day vulnerabilities further reflects our position at the forefront of offensive security.
A tailored, real-world approach
We recognise that every organisation’s environment is different. That’s why every engagement is tailored to your infrastructure, risk profile, and business priorities.
-png.png?width=1500&height=768&name=A%20comprehensive%20tailored%20approach%20(2)-png.png)
Figure: Core penetration testing approaches, covering internal, external, web application, and wireless environments.
Our approach typically includes testing across:
-
-
Internal penetration testing: Simulating insider threats and compromised systems to identify risks within your network.
-
External penetration testing: Assessing internet-facing systems such as firewalls, servers, and applications.
-
Web application testing: Identifying vulnerabilities in applications, including logic flaws and injection risks.
-
Wireless testing: Evaluating Wi-Fi security, encryption standards, and access controls.
-
Red team expertise and offensive security
For organisations requiring a deeper level of testing, our Red Team conducts advanced attack simulations that go beyond traditional penetration testing.
Our team brings real-world experience from industry events and competitive environments, including Capture the Flag (CTF) competitions such as CrikeyCon and BSides. This hands-on expertise helps us uncover vulnerabilities that standard testing approaches may miss.
These engagements replicate how real attackers operate, helping you identify weaknesses across people, processes, and technology.
Manual testing for deeper insights
While automated tools play an important role, they cannot identify every risk.
Our approach places a strong emphasis on manual penetration testing, allowing us to uncover:
-
-
Chained vulnerabilities
-
Business logic flaws
-
Complex attack paths
-
Advanced exploitation techniques
-
This results in deeper, more actionable insights that reflect how real attackers operate.
Supporting services to strengthen your security
Penetration testing is just one part of a broader security strategy.
The Missing Link also provides:
-
-
Incident response: Helping you respond to and recover from security incidents while improving future resilience.
-
Managed security services: Continuous monitoring and threat detection to support ongoing protection.
-
How to get started with penetration testing
Steps to take for a comprehensive test
Getting started with penetration testing does not need to be complex. With a structured approach, you can quickly identify risks and begin strengthening your security posture.
Start with these key steps:
1. Assess your current security posture
Begin by understanding where your risks lie. This can involve an internal review or working with a trusted security partner.
At The Missing Link, our initial consultation helps identify your critical assets, highlight high-risk areas, and establish a clear starting point for testing.
2. Define the scope of testing
Next, determine which systems, applications, and infrastructure should be tested.
Scope should be prioritised based on:
-
-
Business-critical systems
-
Risk exposure
-
Compliance requirements
-
A well-defined scope ensures testing focuses on the areas that matter most.
3. Establish an ongoing testing approach
Penetration testing should not be treated as a one-off activity. As your environment evolves, so do your risks.
Building a regular testing schedule helps ensure vulnerabilities are identified and addressed continuously, rather than reactively.
The Missing Link’s process
Our structured approach ensures your penetration testing delivers meaningful, actionable outcomes:

Figure: The Missing Link’s penetration testing process, from consultation through to post-test support.
1. Consultation: We begin with a detailed consultation to understand your environment, risks, and objectives.
2. Scope definition: We define a targeted testing scope, focusing on the systems and assets that present the highest risk.
3. Testing phase: Our CREST-certified team conducts testing using a combination of manual techniques and advanced tooling to simulate real-world attacks.
4. Reporting and remediation: You receive a clear, prioritised report outlining vulnerabilities, business impact, and recommended remediation steps.
5. Post-test support: We continue working with you after the test, helping implement fixes and strengthen your security over time.
Ongoing protection with The Missing Link
Effective security is an ongoing process. Whether you require quarterly testing for compliance or periodic assessments as your environment evolves, The Missing Link offers flexible testing options tailored to your organisation.
By following a structured and continuous approach, you can reduce risk, strengthen resilience, and stay ahead of emerging threats.
How to select a penetration testing provider
Choosing the right provider is critical to the success of your testing.
When evaluating options, consider:
-
-
Expertise and certifications: Look for qualified professionals with recognised certifications such as OSCP, OSWE, and CREST accreditation.
-
Experience: Proven experience across different environments, industries, and testing scenarios.
-
Methodology: A structured approach that reflects real-world attack techniques.
-
Tools and techniques: A balance of automated tools and manual testing for deeper insight.
-
Reporting quality: Clear, actionable reports that prioritise risk and support remediation.
-
A strong provider should not only identify vulnerabilities but also help you understand and address them effectively.
Securing your future: The lasting impact of penetration testing
Cyber threats are evolving faster than most organisations can respond. A reactive approach is no longer enough.
Penetration testing puts your defences to the test by uncovering hidden vulnerabilities before they can be exploited. Simulating real-world attacks, it highlights critical gaps across your systems, giving you the insight needed to strengthen your security and reduce the risk of costly breaches and operational disruption.
As threats continue to grow in complexity, security must become an ongoing process. Regular penetration testing ensures your defences remain effective, helping your business stay ahead of emerging risks and adapt to an ever-changing threat landscape.
At The Missing Link, we act as a long-term security partner, delivering tailored penetration testing backed by deep technical expertise. With CREST-certified professionals and our status as one of Australia’s only CVE Numbering Authorities, we go beyond identifying vulnerabilities to provide actionable insights and ongoing support that strengthen your security over time.
By working with The Missing Link, you gain more than a service provider. You gain a partner committed to protecting your business, supporting your team, and helping you build a resilient security posture for the future.
Ready to take the next step?
If you’re looking to better understand your risks and strengthen your defences, our team can help you get started with a tailored penetration testing approach.
FAQs
The cost of penetration testing varies depending on the scope, complexity, and type of assessment required.
Key factors include:
- The number of systems or applications being tested
- The depth of testing required
- The type of engagement, such as network, web, cloud, or Red Team testing
Penetration testing should be viewed as an investment in reducing long-term risk, rather than a one-off expense.
Penetration testing typically uncovers a mix of technical and configuration-related issues, including:
- Misconfigured access controls
- Weak authentication mechanisms
- Unpatched or outdated systems
- Insecure APIs or web application flaws
- Poor network segmentation
Many of these vulnerabilities require manual testing to be fully identified and understood.
Yes. Internal and social engineering testing can simulate scenarios where an attacker gains access through compromised credentials or insider activity.
This helps organisations understand:
- How far an attacker could move within the network
- What systems or data could be accessed
- Where controls such as segmentation or privilege management may be insufficient
Once vulnerabilities are identified, they are prioritised based on risk and potential impact.
From there, organisations can:
- Apply patches or configuration changes
- Strengthen access controls
- Improve monitoring and detection
- Update security policies and processes
Follow-up testing is often conducted to confirm that vulnerabilities have been successfully resolved.
When properly scoped and managed, penetration testing can be safely performed on production environments.
An experienced provider will:
- Define clear rules of engagement
- Avoid high-risk actions unless approved
- Coordinate testing to minimise disruption
The goal is to simulate realistic attack scenarios without affecting business operations.
A security audit reviews policies, configurations, and compliance against established standards.
Penetration testing goes further by actively attempting to exploit vulnerabilities to demonstrate real-world risk.
- Audits highlight potential gaps
- Penetration testing shows how those gaps could be exploited
Both approaches are valuable, but penetration testing provides a deeper understanding of how an attack might unfold.
Latest insights
Author
As Application Security Manager at The Missing Link, I help development teams bake security into every stage of the software lifecycle. With a background in secure coding and deep experience testing high-stakes applications, I bring a pragmatic, developer-first mindset to modern AppSec challenges. From training and tooling to source code reviews, my focus is on building secure systems without slowing teams down. When I’m not at the keyboard, I’m usually in the gym lifting heavy things.



